Yesterday, Apple disclosed for the first time that it is working to develop a software tool to detect and remove the Flashback malware from infected machines. We also previously profiled Flashback Checker, a simple app designed to allow users to easily see if their Macs are infected but which provides no assistance with disinfection.
While Apple works on its own official solution, other parties have continued to develop their own increasingly user-friendly tools for dealing with the threat and cleaning infected machines, with some of those tools making their way into the public's hands.
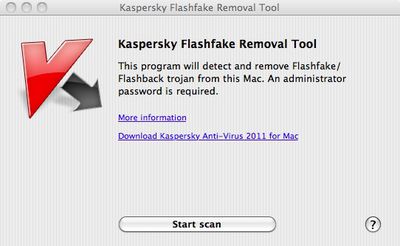
Russian antivirus firm Kaspersky Lab, which has played a key role in monitoring and publicizing the threat of Flashback, yesterday announced the launch of a free web-based checker where users can simply input the hardware UUID of their Mac to see if it has registered on the firm's servers as an infected machine. The company has also released Flashfake Removal Tool, a free app that quickly and easily detects and removes the malware.
Antivirus firm F-Secure has also announced its own free Flashback Removal app. The app generates a log file detailing whether it has found Flashback on a user's system, and if so quarantines it inside an encrypted ZIP file for disposal.
F-Secure also points out that Apple has yet to offer any protection for users running systems earlier than Mac OS X Snow Leopard. Flashback uses a vulnerability in Java to install itself without user authorization, and Apple released software patches for Java on Lion and Snow Leopard last week to close that hole and prevent infection on updated systems. Machines running earlier versions of Mac OS X do, however, remain unprotected. Specifically, F-Secure notes that over 16% of Macs are still running Mac OS X 10.5 Leopard, marking a substantial user base that remains vulnerable to the threat.
Update: Kaspersky Lab has informed MacRumors that the Flashfake Removal Tool has temporarily been pulled after the discovery that in some cases it could erroneously remove certain user settings. A fixed version of the tool will be posted as soon as it is available.
Update 2: The patched version of the Flashfake Removal Tool is now available through the Kaspersky Lab site.


















Top Rated Comments
I think in time they will try to get you to open your walletsky so you can spend some of your moneysky on their Mac anti-virusky.
A few days ago I did the Terminal commands that F-Secure posted for checking for Flashback trojan (http://www.f-secure.com/v-descs/trojan-downloader_osx_flashback_i.shtml). Redid it today and both times came up negative.
I downloaded and used an app to do the same (https://github.com/jils/FlashbackChecker/wiki) and also the F-Secure Flashback Removal app. They both also came up negative.
I used the web-based checker in this article, put in the hardware UUID of my Mac and surprise, surprise, it came up positive.
I would have thought that MacRumours would've tested them and saw that the Kaspersky Lab web page is bogus!!!!
People who don't admit that "virus" and "malware" mean the same thing to most people miss the point.
If your identity and credit card numbers are sent to criminals in the Ukraine - is it "OK" if malware sent the info and "bad" if a virus sent the info?
I'd think that most people would label it as "bad" regardless of minor technical details of the infection.
And add to that the simple truth that viruses aren't really that common anymore - OS changes have made the threat of viruses fairly small. When you get a product like Norton, you're buying "anti-malware" protection - even if the product name contains the word "antivirus" for historical familiarity.